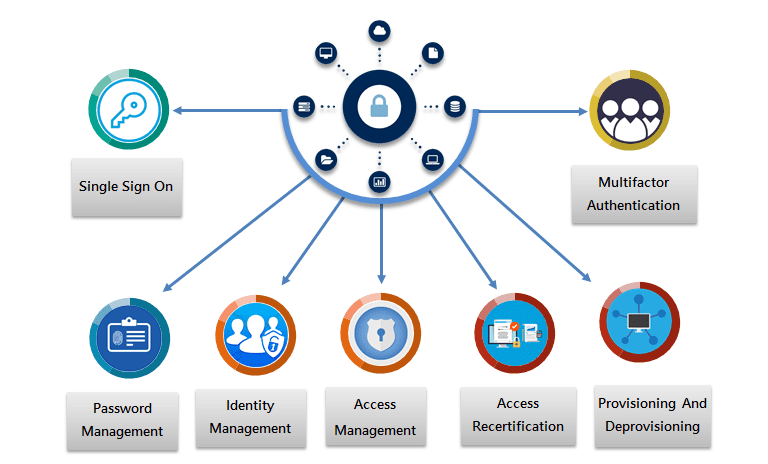
Access Governance
Access Governance is a combined model of process and technology to manage and secure access for the enterprise resources. It plays a key role in developing security infrastructure.
IT professionals with evolving roles recognize that managing and controlling security environment can be more challenging. LTS Secure recognizes that, Access Governance Suite capabilities will continue to leverage technologies to realize higher benefits versus the costs incurred. User demand will continue to drive the discipline to transform from a compliance-based program into a true business enabler (e.g., Access Recertification and Identity Management is a key component for rolling out B2C applications, that will drive operational efficiencies and improve the user experience) while helping to reduce risks created by emerging technologies and threats.
As Identity and Access Management Governance continues to evolve, organizations will look for broader, enterprise-based solutions that are adaptable to new usage trends such as mobile and cloud computing.
Core Features
Seamless Access Experience Via LTS Secure SSO (Single Sign-On)
LTS Secure Single sign-on (SSO) is a centralized operation and user authentication service to develop a single set of login credentials to access multiple access applications. Apps like office 365, Zendesk, Google apps and thousands of other modern other enterprise apps bring unprecedented ease of use and cost advantages. These apps also bring challenges because they are outside of the firewall and disconnected from on-prem directories.
IT teams often to struggle to provide secure access to these apps for their employees or customers.
Benefits
- Scalability
- Automated credential management
- Rapid provision for cloud first application Log monitoring
- Better access management

LTS Secure Authentication With Multi-Factor Authentication
LTS Secure Multi-factor authentication (MFA) is a simple and best practice that adds an extra layer of security that allows companies to protect against the data breach and compromised credentials. Users provide extra information or factors when they access corporate applications, networks, and servers.
LTS Secure Multi-factor authentication is a combination of the following factors.
- Username, password, PIN or security questions
- Smartphone, one-time passcode or Smart Card
- Biometrics, like your fingerprint, retina scans or voice recognition
Benefits
- Secure authentication for all environments
- Comprehensive second factors and assurance levels
- Adaptive and risk-based capabilities
- Fully integrates with your organization

Enforce Strong Credential Policies With LTS Secure Self Service Password Management
Self Service Password Management helps you to enforce strong credential policies so you can reduce potential breaches as a result of poor password practices. With strong password management users confirm their identity using a wealth of customizable verification techniques including two-factor authentication.
LTS Secure Self Service Password Management is a convenient, user-friendly, web-based password management solution that substantially reduces password-related help desk tickets.
Benefits
- Self-reset passwords
- Self-unlock accounts
- Password expiration notification
- Password synchronizer
- Password policy enforcer
Manage User Identity And Their Role And Entitlements With LTS Secure Privilege Identity Management
LTS Secure Privileged Access Management enables IT organizations to reduce the risk of security breaches by minimizing the vulnerable attacks. LTS Secure Privileged Access Management solutions help you to consolidate identities, deliver cross-platform, privilege access and control shared accounts, while securing remote access and auditing all privileged sessions.
Benefits
- Minimize the attack surface with just-in-time privilege
- Enable intelligent, automated, real-time decisions for granting privileged access
- Save cost with an integrated solution for privileged identity management (PIM)
- Enable cost-effective compliance and auditing

Equip User Account With LTS Secure Provisioning And De-provisioning Feature
Provisioning means furnishing access for a new user account and de-provisioning means revoking all access of the users. Also to synchronizing user attributes across multiple directories. LTS Secure provisioning features enable you to manage user accounts automatically within an application.
Benefits
- Centralized account management
- Bulk of user data import from various sources.
- Advance configuration rules and workflow
Improve Audit Process With LTS Secure Access Recertification
LTS Secure Access Recertification involves auditing user privileges and access details, also to determine whether they are following correct internal policies and compliance regulation. With LTS Secure Access Recertification, you can determine, how often users certifying their requirement for an account or membership. The policy also defines the function that occurs if the user does not respond to the recertification request.
Benefits
- Reduce the amount of time and budget devoted to access certification
- Centralize data repository by integrating target and source systems
- Replace spread sheets with web-based interface to approve or reject access and log actions
- Reduce the security and compliance risk associated with unauthorized access
- Document the certification effort and quickly share the evidence with auditors