Negligee Insider
A Negligee Insider is an employee or contractor with privileged access to an IT system. It puts the organization at risk because it is not compliant with the IT system. Exposing. Regulatory IT procedures.
The power-integrated UEBA is a security UEBA Solution that uses innovative analytical technologies such as machine learning and deep learning to discover unusual and dangerous behavior by users, machines, and other entities on corporate networks.
User and Entity Behavior Analytics (UEBA) is a security solution that uses innovative analytics technologies such as machine learning and deep learning to detect unusual and dangerous behavior from users, machines, and other entities on the business network.
If the UEBA system detects a malfunction, it alerts InfoSec staff and allows InfoSec staff to continue their investigation.
A Negligee Insider is an employee or contractor with privileged access to an IT system. It puts the organization at risk because it is not compliant with the IT system. Exposing. Regulatory IT procedures.
A malicious insider is an employee or contractor with privileged access to an IT system attempting to cyber-attack a company. It is challenging to measure malicious intent or detect it from log files or regular security events. UEBA solutions help establish a baseline of typical user behavior and detect anomalous activity.
It is common for an attacker to break into an organization, compromise a privileged user account or trusted host on the network, and continue the attack from there. UEBA solutions help you quickly detect and analyze malicious activity performed by attackers through compromised accounts.Traditional security tools detect compromised insiders if the attacker's pattern or kill chain is currently unknown or if the attack moves laterally within the organization by changing credentials, IP addresses, or machines. I do it hard. However, UEBA technology can detect these attacks because it forces assets to behave in most cases differently from the established baseline.
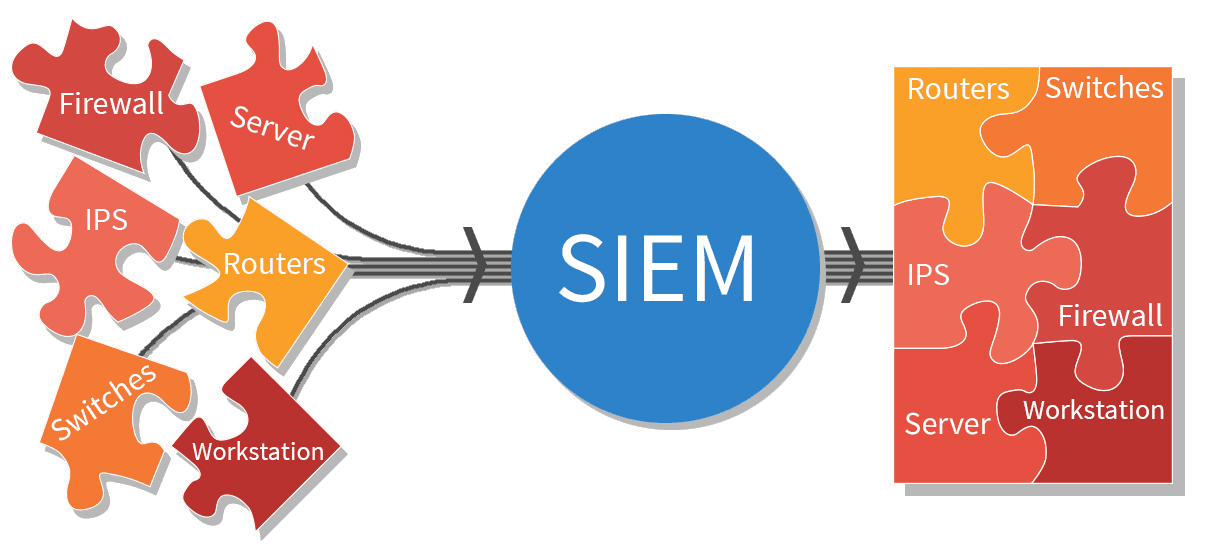
SIEM solution collects events and logs from multiple security tools and critical systems and generates many alerts for security personnel to investigate. This leads to alert fatigue, a common challenge for Security Operations Centers (SOCs).SIEM solutions can streamline security workflows and extend operations.
UEBA solutions help you understand which incidents are exceptionally unusual, suspicious, or potentially dangerous in the context of your organization. UEBA can go beyond baselines and threat models by adding data about organizational structure (for example, asset importance, roles, and access levels for specific administrative functions). A slight deviation from the standards of a tightly protected system or top-level administrator may be worth looking for an investigator. For the average employee, only significant variations receive high priority.
User and Entity Behavioral Analytics (UEBA) helps security analysts easily spot suspicious behavior and identify security incidents that other solutions are missing.
Using advanced machine learning, UEBA creates a baseline of normal behavior for each user, peer group, and entity in the network, rather than applying predefined rules to the default behavior. Increase. By assessing activities that deviate from these baselines, UEBA detects strange and dangerous behavior that is not immediately apparent. Set up user and machine risk assessments and compare usage behavior with competitors.
Log point UEBA calculates risk scores in the range 0-100 rather than on a variable scale, so security analysts can easily prioritize risk scores. The closer the value is to 100, the higher the operation risk.
UEBA provides tailored detection for selected users and entities, making it easier for analysts to identify, prioritize, and manage anomalies. We support analysts by significantly reducing threat hunting time, reducing alert fatigue, and allowing you to focus on managing threats that require your attention.CASB products support the use of cloud apps from secure or unmanaged devices.UEBA security solutions safeguard your company from internal threats.
