SOC in Cyber Security
Know SOC as a Service
A Unified Platform for Enterprise Cyber Security.
Accustomed with SOC as a Service with LTS Secure
Stay Protected with a 24/7 SOC as PaaS that responds and scales as fast as you do.
LTS Secure’s vSOCBox™ platform (SOC as PaaS) provides an integrated, comprehensive, and unified threat detection and response capability with concerted effort to cover all cyber security risks and enable a risk-free business.
SOC as a Service
Cybersecurity breaches are no longer seasonal but climate-influenced. No matter the size or type of organization, a dedicated team should have the right skills and tools to identify flaws and defend against these cybersecurity breaches. LTS Secure strives to ensure customers are protected from digital and cyber threats while removing the pain of their CAPEX and OPEX investments. LTS Secure has constantly improved various companies’ digital and cyber security posture through its world-class SOC services. SOC in cyber security is to monitor, prevent, detect, investigate, and respond to cyber threats 24/7.
What is SOC as a Service?
SOC as a Service (SOCaaS) is a subscription-based managed threat detection and response model that provides any organization with a best-in-class Security Operations Center.
Social offers all the benefits of a dedicated 24/7 SOC. Without the prohibitive costs, complexity, and frustration of building, staffing, and managing a single company. A managed SOC service enables organizations to offload the people, processes, and advanced technology required to operate and manage a SOC externally and deliver it as a cloud-based service.
Organizations of all sizes need protection and expertise to monitor threats. SOC as a Service offers organizations an affordable way to get an end-to-end detection and response solution for today’s SOC challenges. Today’s advanced threat demands intelligent and automated Cyber Security Solutions.
What is SOC as a Service?
SOC-as-a-Service goes beyond what traditional Managed Security Service Providers (MSSPs) and Managed Detection and Response providers offer. Traditional MSSPs can offer advanced Security Operations Center (SOC) capabilities for threat detection and response.
SOC as-a-Service offers many benefits, including:
Faster Detection and Remediation
SOC-as-a-Service providers reduce the burden on internal security teams. We monitor your security 24/7, use automation and data science to accelerate detection, and deliver trusted alerts. Higher confidence indicators mean quicker and extra efficient detection and remediation.
Cyber Risk Mitigation
Working with a SOC-as-a-Service provider reduces the risk of compromise and potential cost and brand damage associated with a successful attack.
Increase Business Agility and Scalability
Between IoT and remote work, acquisitions and service expansion, businesses are growing and changing faster than ever. SOC as a service supports fast growth by enabling organizations to modify and scale their outsourced SOC consumption as needed to meet their priorities.
Cost Savings
Organizations pay SOC as a Service monthly operating expense based solely on usage. For most companies, this is cheaper than the capital and operational costs of setting up and staffing an on-premises SOC.
Why Should I Choose SOC as a Service Instead of Building My Own?
It is an important decision. An effective SOC is the most important security element for an enterprise, operating 24×7 to detect and prevent threats before they harm and respond quickly when attacks bypass security controls.
There are several important considerations when deciding whether to run your own on-premises SOC or work with an enterprise SOC-as-a-Service provider.
Technology
SIEM Security forms the technical backbone of the SOC. However, as the threat landscape changes, organizations often have new and updated layers of tools. Procure, deploy, configure, integrate, update, and maintain the various products required to run an effective SOC.
People
Nearly 80% of organizations do not have a sufficiently qualified analyst to lead their SOC. Aside from analysts, hiring skilled professionals in threat hunting, incident response, security engineering, and more is difficult.
Compliance and Certification
Protecting and protecting data is a business imperative. Organizations must maintain high standards to prevent breaches. SOCs must comply with ISO 27001 or SOC II Type 2, and in certain industries, other regulations or frameworks such as HIPAA, GDPR, CCPA, PCI DSS, and NIST. Achieving and continuously demonstrating compliance is a time-consuming and expensive process that should include in the SOC's total cost of ownership.
Effectiveness
According to Ponemon, the average cost of a highly effective SOC is $3.5 million, compared to $1.96 million for a very low effective SOC. However, effectiveness requires more than funding. Detecting, investigating, triaging, and remediating threats requires the right people, processes, and tools. These threats are constantly evolving, so employees must constantly learn and regularly review and update their tools. It takes effort and human knowledge to run a strong and capable SOC.
Facility
Traditionally, the Security Operations Center (SOC) is a dedicated office space where professionals work and collaborate. The cost of securing, providing, and securing space for a sufficient number of staff with 24-hour air conditioning can be substantial. A 24/7 safety operations center (SOC) has long been considered an important part of a powerful cybersecurity strategy. But SOC implementations tend to be very complex and luxurious, putting a contemporary SOC out of reach for many companies. It can take years to emerge as operational, with expenses inside.
The LTS Secure Products
Next-Gen SIEM
Enable detection, prevention & remediation of advanced threats
CASB
A unified security control for your organization
IDM
Control user access to critical information
UEBA
Strengthen Network Security with UEBA
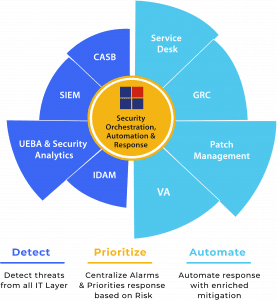
SOAR
Security, Orchestration, Automation, & Response
Why LTS Secure vSOCBox™ Platform?
Instant Access to Security Expertise
Vendor Agnostic Approach
Cost-effective security
Extension of Your Team
Cutting-edge Technology
The LTS Secure vSOCBox™ Platform includes:
Fully managed advanced SOC built on SIEM platform
External & internal vulnerability scanning at regular intervals
24*7 monitoring for cloud infra, network, users, & App
Advanced Threat Detection Services
Expert Forensic Investigation Services
Compliance Control, Mapping, and Management
Automated Remediation
Round the clock support
Incident Response Services
The acceptance of "SOC as PaaS" has been driven by-
01.
Continuous visibility of Network, Application & Users needs established processes.
02.
Security Solution alarms are delivered in non-integrated silos, increasing costs
03.
The desire to get more value out of existing security investments.
04.
Lack of skilled Security Resources increasing challenges to Setup SOC.
05.
Need to expand security monitoring to include cloud, OT, and IoT devices.
The LTS Secure vSOCBox™ Platform Benefits:
73%
Reduce business continuity risk
28 Min to 7 Min
Reduce Threat response Time
55%
Reduce Cost for an Audit
60%
Reduction in False Positives
LTS Secure “Amplify Partner Program” Value
Proposition for Partners
The LTS Secure’s SOC Platform as a Service (SOC PaaS) platform, vSOC Box™, will help you to quickly launch your own scalable, automated, and highly cost effective SOC Operations. Leverage one of a kind SOC-platform as-a-Service (SOCPaaS) offering from LTS Secure and take a holistic approach in implementing innovative strategies that will provide a cohesive protection to your customers.
Solution as Module
Established SOC Process
Security Incident Team 24 * 7
Updated Threat Intelligence
Portfolio Addition
Revenue Increase